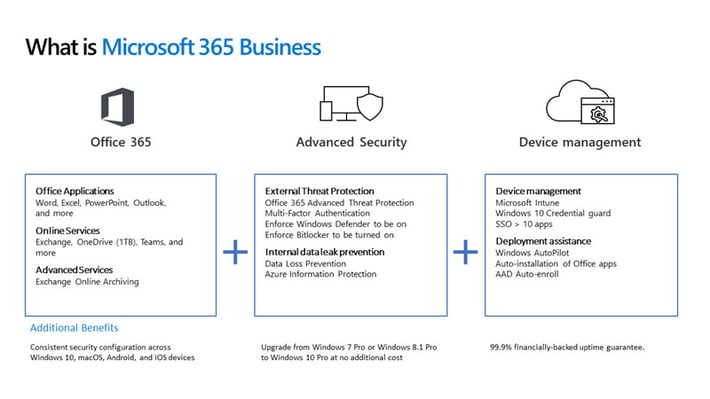
Microsoft 365 is an integrated solution that includes Office 365 and Windows 10 Enterprise, plus enterprise-level mobility and security features. Because of the included security features of Microsoft 365, you can save money by upgrading from Office 365 to Microsoft 365.
Advanced Security Features
Microsoft 365 comes with leading-edge security capabilities that protect your business, empowering your employees to be productive from anywhere, on any device.
Today's dynamic workplace requires tools that foster collaboration and support employees remotely. Microsoft 365 Business keeps company data secure while ensuring employees are their most productive, in the office or on the go.
Windows 10
By migrating your employees' workstations to Microsoft 365, you also standardize on Windows 10, the most secure Windows platform ever. Plus, Microsoft 365 Business adds cloud-based management, which helps ensure that your devices are properly configured to take advantage of the security innovations in Windows 10 and significantly reduces your company's risk profile.
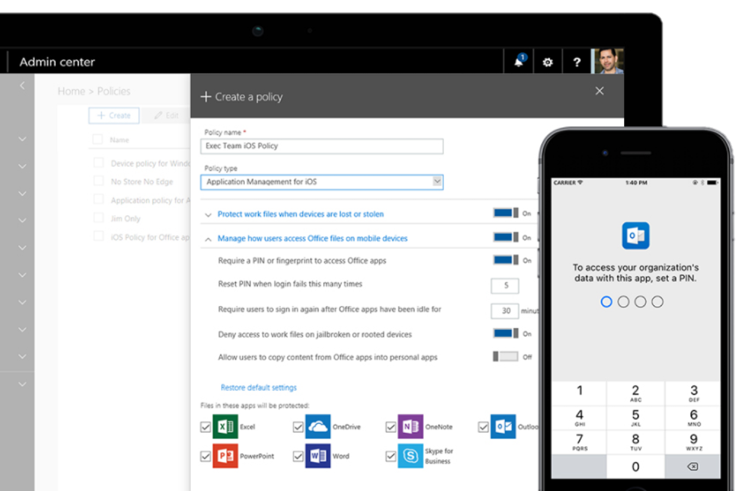
Mobile Device Management
Microsoft 365 Business also includes mobile application data and device management, including your employees' personal devices. With this functionality, when an employee leaves the company or loses their personal mobile device, your company data remains protected, and your employee's private data remains private. Because Microsoft 365 Business is cloud-based, it is always up to date with the latest security protection and features.
Microsoft 365 Security Features
Key security features in Microsoft 365 include:
- Office 365 Advanced Threat Protection
- Azure Information Protection P1
- Intune
- Data Loss Prevention
These features alone highlight the value of upgrading to Microsoft 365 Business. The cost of these combined equal $34.50. Yet you can buy Microsoft 365 Business for $20 and get even more.
Microsoft 365 Business safeguards your data by protecting your company against external threats such as phishing attacks and malicious emails. It also includes features that prevent sensitive information such as social security numbers and credit card information from leaving the organization.
Employees working remotely carry a vast quantity of corporate data on their mobile devices, exposing your business to risk. The simplified device management in Microsoft 365 provides enterprise-level security that protects you.
A Layered Approach to Security
Microsoft 365 protects your company against external threats and data leaks by taking a layered approach to security that covers three areas.
Protection from threats
You get protection from sophisticated threats hidden in email attachments and links and cutting-edge defenses against zero-day threats, ransomware, and other advanced malware attempts.
Protection from data leaks
You get protection from data leaks to prevent sensitive information such as social security numbers and credit card numbers from being shared outside your business.
Control data access
You can control and manage access to information by applying restrictions such as "do not copy" and "do not forward." You gain the ability to remotely wipe data on lost or stolen mobile devices without impacting personal information.
How Does Security Work in Microsoft 365?
The top layer of security in Microsoft 365 focuses on protecting your business from external threats by giving you access to enterprise-grade service and protection. These threat protection tools keep your business free of hazards such as spam, malware, viruses, phishing attempts, and malicious links while protecting you from sophisticated threats such as zero-day ransomware and other advanced threat techniques.
Protection from Threats with the Advanced Threat Protection Feature
Today, virus and malware attacks are a common occurrence. When successful, these attacks can cause several issues for a company — from loss of customer trust to financial woes resulting from business-threatening downtime and more.
With Microsoft 365:
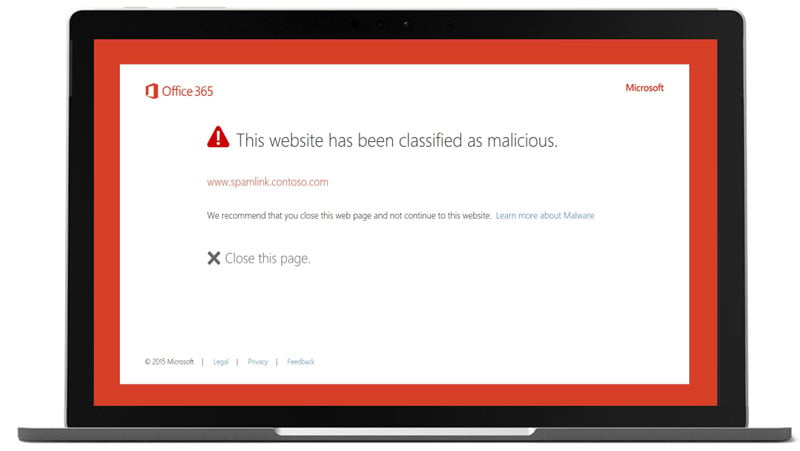
Links are checked in real-time to warn you if a website destination is a malicious site.
Any security program will scan the links in your emails to see if they'll redirect to a malicious site. However, a particularly clever phishing attack will send an email that contains harmless links, but then, after that message hits your inbox, it will detect that it passed your filters and change those links to something malicious. The Safe Links feature in Microsoft 365 double-checks every link when you click on it to see if you're about to be sent somewhere dangerous.
AI-powered attachment scanning detects malware previously not seen.
With this feature, every email attachment that your company receives is opened in a virtual environment to see what happens next. If strange behavior indicates that a cyberweapon is deployed, that file will never reach the intended recipient's inbox.
Windows devices are monitored for suspicious processes such as ransomware.
This tool learns how everyone in your organization communicates (and who they communicate with) so that when an unnatural or unusual string of communications begins, the system can accurately gauge that one of those accounts is being controlled by an attacker.
Advanced Threat Protection (ATP) Feature
The Advanced Threat Protection (ATP) feature protects organizations from malicious attacks and malware.
The ATP feature includes email attachment scanning, URL scanning in emails and Office documents, and proofing intelligence in email messages. It also includes the anti-phishing capability to detect when someone attempts to impersonate users or an organization's domain.
In addition, the ATP feature blocks malware in SharePoint, OneDrive, and Microsoft Teams.
Even if your staff understand that they shouldn't click on hyperlinks sent from people they don't know, they can be tricked by today's sophisticated phishing schemes. The ATP feature protects your users from clicking through to malicious or unsafe sites.
The ATP feature scans every email attachment. It performs a comprehensive, real-time analysis of the behavior of the file to determine its intent (whether normal or malicious), which leads to more intelligent protection against unsafe attachments that form the basis for phishing schemes and ransomware infections.
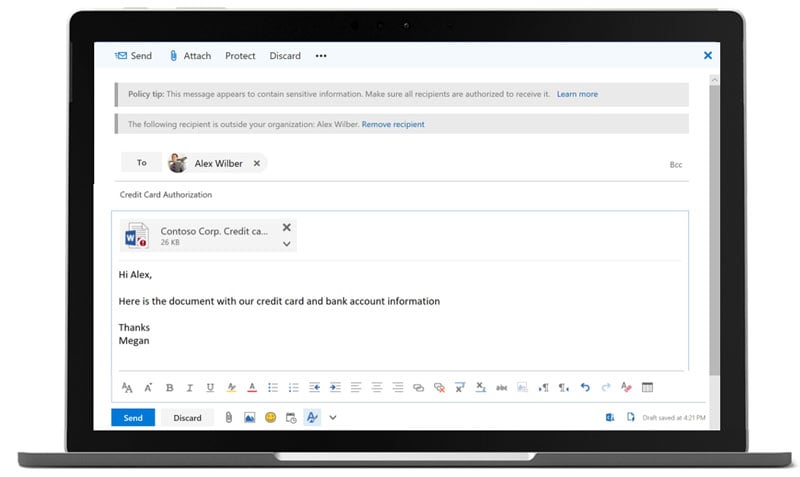
Protection from Data Leaks with the Data Loss Prevention and Intune Features
Organizations handle sensitive information such as credit card numbers, social security numbers, dates of birth, and intellectual property critical to business operations. Keeping this information safe is a challenge.
With Microsoft 365:
- You can apply data loss prevention policies to keep sensitive information from falling into the wrong hands.
- You can use device encryption to protect data if a computer is lost or stolen.
- You can manage all your devices, including PC, Mac, iOS, and Android.
Data Loss Prevention (DLP) Feature
The Data Loss Prevention (DLP) policies in Microsoft 365 Business enable you to identify easily, monitor, and protect sensitive information through deep content analysis. Using preconfigured templates, we can detect the communication of specific types of sensitive information or personally identifiable information (PII).
With the DLP feature, you can prevent sensitive information from inadvertently leaking outside your organization. This includes credit card numbers, social security numbers, health information, or any other sensitive information. The DLP feature is very useful for any company with compliance concerns that must comply with mandates such as those for NIST, HIPAA, or PCI DSS.
DLP is a policy-based feature. You can set policies for any location (such as Exchange, SharePoint, and OneDrive) and create rules that dictate what happens when data is shared outside the organization. You can block access at all levels and send notifications to the appropriate people, such as the company's compliance officer. This feature includes templates that can conform to geographic or industry-specific regulatory requirements.
Intune Feature
Intune protects corporate data on mobile devices via a container policy. Users cannot share data from the corporate app container to their personal app container.
This feature protects the organization from risky employee activities, whether intentionally malicious or careless. If an employee suddenly terminates their position with the company or loses a device, you can remove all corporate data from the employee's mobile device with one click.
In Microsoft 365 Business, Intune uses a configuration wizard to ensure all managed devices are enrolled in baseline security policies. You can also create custom policies as needed.
Control Data Access with the Azure Information Protection Feature
Businesses are challenged to manage who has access to the company's sensitive information without hindering productivity. Information protection policies in Microsoft 365 enable you to control and manage how information is accessed — ensuring only people who should have access do have access.
With Microsoft 365, you can:
- Require a PIN or fingerprint before accessing business documents and data
- Classify sensitive information as "confidential" and restrict how it can be shared inside and outside the business
- Remotely wipe business data from a device without affecting personal information
- Apply encryption and restrictions such as "do not forward," "do not copy," and "do not print" to emails and documents
Azure Information Protection (AIP) Feature
The Azure Information Protection (AIP) feature in Microsoft 365 enables users to classify information based on sensitivity for the purpose of limited access. You can define who can access data and what they can do with it, such as allowing recipients to view and edit files but not print or forward them.
Users are notified when a recipient receives their message. If a recipient tries to take an action that's not allowed (such as forwarding a document), the AIP feature blocks the attempt and notifies the sender.
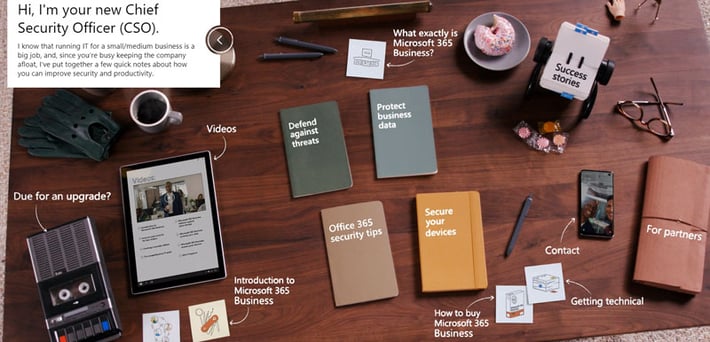
Microsoft 365 Safeguards Your Business
Click the image below to learn more about how using Microsoft 365 helps you improve your security posture.
Microsoft 365 safeguards your business in three ways:
- You get protection from sophisticated external cyber threats hidden in email attachments and links, plus cutting-edge defenses against phishing, spoofing attacks, ransomware, and other advanced malware attempts.
- You gain more control over company data and documents. You get protection from data leaks to prevent sensitive information such as social security numbers and customer credit card numbers from being shared outside your business. You control access to documents, even after those documents have been shared outside your company.
- You can manage the apps, data, and documents on devices that access company data, regardless of the device type or operating system: iOS, macOS, Android, or Windows. Microsoft 365 enables you to manage all devices.
Upgrade to Microsoft 365
There is no better time to upgrade. For the same cost of what you are paying for the combination of Office 365, Windows OS, and advanced security, you get more features and more protection.
Outsourcing the migration of Microsoft 365 to Corserva will save you time and money in the long run. Moving forward, we can also provide Microsoft 365 managed services. We include technical support for all your users 24x7x365 from our US-based help desks.
Get a quote now for our Microsoft 365 migration services.