Since the initial announcement of CMMC, suppliers working in federal supply chains have been anxious to take the steps required to achieve CMMC compliance. Unfortunately, it's been a "hurry up and wait" situation. Until now.
With the announcement of CMMC 2.0 on November 4, 2021, the DoD has introduced changes in the methods to achieve CMMC compliance, which includes new options for self-attestation for some companies.
At the same time, the Cybersecurity Maturity Model Certification Accreditation Body (CMMC-AB) is starting to approve Certified 3rd Party Assessor Organizations (C3PAO) as authorized C3PAOs. As more candidate C3PAOs become authorized C3PAOs, Organizations Seeking Compliance (OSC) will be able to step up their compliance efforts and get a CMMC assessment.
CMMC Compliance Checklist
- Determine the level of CMMC certification (Levels 1 – 3) you will need. At a minimum, you will need to meet Level 1 of CMMC, which can be accomplished through self-attestation.
- Limit the amount of CUI you receive in fulfillment of a contract. As much as possible, isolate CUI.
- Refer to NIST SP 800-171 to determine where your company falls short in the cybersecurity best practices. NIST 800‑171 is equivalent to CMMC Level 2. Develop System Security Plans and Plans of Actions with Milestones (POA&M).
- Perform remediation to close any gaps identified in POA&Ms.
- Some Level 2 companies will be able to self-certify to compliance, and others will need to hire a C3PAO to perform a CMMC assessment.
1. Determine Your CMMC Level
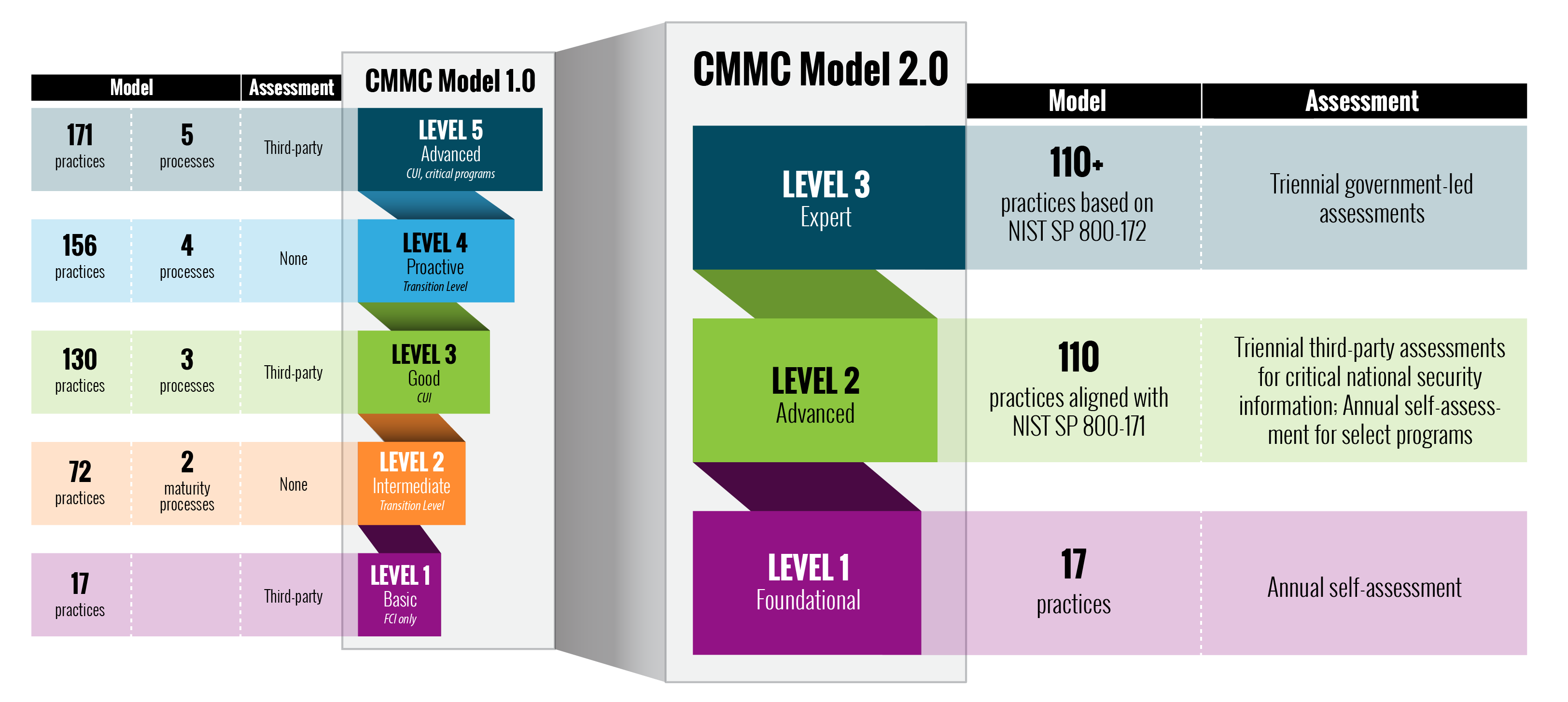
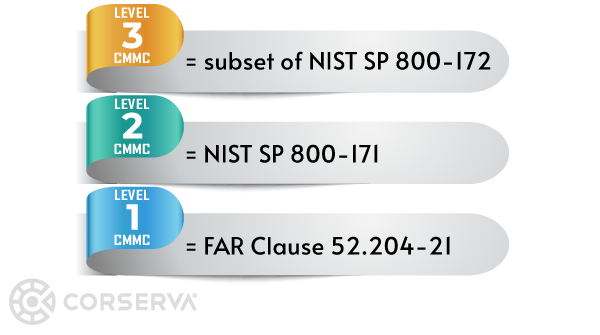
The CMMC framework contains 3 maturity levels.
- Level 1 – all Level 1 companies can self-certify
- Level 2 – a subset of Level 2 companies will be able to self-certify and others will need to hire an outside assessor (C3PAO) to perform an assessment
- Level 3 – all Level 3 companies will require a government-led assessment
Although there were 5 levels in Version 1.0 of CMMC, that has changed to 3 levels with the announcement of CMMC 2.0.
FCI and CUI
The level of CMMC you need to meet depends on the contract under which you are working.
- If you deal with Controlled Unclassified Information (CUI), you must meet Level 2 or 3 of CMMC.
- If you are only protecting Federal Contract Information (FCI), your requirement will only be for Level 1 of CMMC.
Flow Down Clauses
You do not necessarily need to meet the same level of CMMC as the contractor under which you are working. It is possible you may only need to meet Level 1, while the contractor under which you are working may need to be at Level 2.
Typically, prime contractors are notified by the Department of Defense (DoD) directly that they need to comply with CMMC. Flow-down clauses within the contract will stipulate that any subcontractors of the prime also need to comply.
CMMC Requirements
The DoD is in the process of migrating from NIST 800-171 to the CMMC framework and by October 1, 2025, all new DoD contracts will require CMMC. No existing contracts will have CMMC requirements inserted into them.
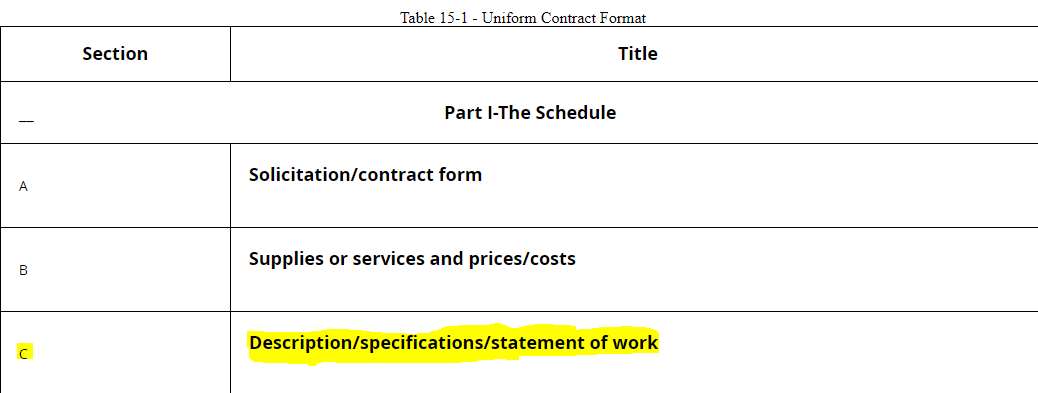
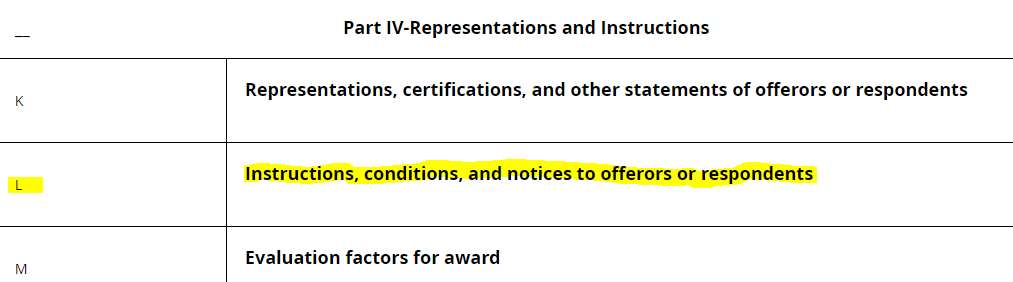
If a contract requires CMMC, it will be included in the RFP in section C ("Description/specifications/statement of work") and section L ("Instructions, conditions, and notices to offerors or respondents").
If there are future contracts for which you plan to bid, you will want to be certified to the level of cybersecurity required by the contract, RFI, or RFP. You can also base your decision as to which level to certify on internal business goals.
2. Isolate CUI
Since CMMC focuses on the protection of CUI, it makes sense to limit the exposure.
Determine where you currently store CUI within your company and its systems. Look for ways to reduce the amount of CUI you have. If a prime contractor or other contractor sends you CUI, try to limit the amount of CUI you receive to only the data required for you to do your work.
The less CUI you have, the easier it will be to protect it.
3. Develop Plans of Actions with Milestones (POA&M)
Before a C3PAO assessment, you can internal review your IT environment or hire an outside company to do this for you.
The pre-assessment will identify areas for remediation.
- Level 1 companies must comply with 17 cybersecurity best practices.
- Level 2 companies must comply with 110 best practices in NIST 800-171.
- Level 3 companies must comply with over 110 best practices based on NIST 800-172.
To show compliance with NIST 800-171 and prepare for CMMC, you develop and maintain formal documents for submission to DoD prime contractors or subcontractors upon contract initiation or renewal. These documents include a System Security (SSP) and Plan of Action with Milestones (POA&M).
A POA&M identifies areas for remediation and how you plan to correct deficiencies.
You can hire an outside company, such as Corserva, to perform a pre-assessment of your IT environment and develop SSPs and POA&Ms for you.
4. Perform Remediation
Once you have determined what remediation needs to take place in order for your company to comply with CMMC, you implement the process and technology changes required.
Your POA&M serves as a roadmap of where you have gaps that need to be filled.
You can perform the remediation with internal resources or hire an outside IT company, such as Corserva, to execute the process and technology changes needed.
5. Hire a C3PAO to Perform a CMMC Assessment or Self-Certify
Level 1 CMMC
Level 1 companies can self-certify to CMMC compliance annually.
Level 2 CMMC
Some Level 2 companies will be able to self-certify to CMMC compliance, and others will require an outside third-party assessment.
- Level 2 contractors who do not handle information deemed critical to national security can perform annual self-assessments to comply with CMMC.
- Level 2 contractors managing information critical to national security are required to undergo third-party assessments every three years.
Level 3 CMMC
All Level 3 companies require a government-led assessment every three years.
Research and Hire a C3PAO
Companies working in federal supply chains can achieve CMMC compliance by completing a CMMC assessment performed by a Certified 3rd Party Assessor Organization (C3PAO).
As the Organization Seeking Compliance (OSC), your company hires the C3PAO to perform your CMMC assessment.
C3PAOs are authorized by the CMMC-AB to perform assessments.
The CMMC-AB Marketplace lists C3PAO companies. Only the companies listed here as authorized C3PAOs are approved by the CMMC-AB to perform assessments.
Companies listed in the CMMC-AB Marketplace as candidate C3PAOs have begun the process to become an authorized C3PAO, but have not yet completed the process.
Use the CMMC-AB Marketplace to research potential C3PAOs. Only hire a C3PAO that is listed as an authorized C3PAO on the Marketplace.
The CMMC-AB is the only organization that can qualify a C3PAO to perform CMMC assessments. Note that the CMMC-AB does not perform assessments directly. Instead, C3PAO companies are certified by the CMMC-AB to perform assessments.
The cost for a CMMC assessment will depend upon several factors, including your IT infrastructure's certification level and complexity.
CMMC Assessment Process
Once you've hired a C3PAO company, you will schedule the assessment with the C3PAO.
The process for a CMMC assessment is as follows:
- Hire a C3PAO to perform the assessment.
- The C3PAO performs the assessment of your company.
- The C3PAO creates an assessment report.
- If there are no deficiencies, the C3PAO issues a CMMC certificate.
- The C3PAO submits a copy of the assessment report and CMMC certificate to the DoD. The CMMC certificate is valid for three years.
- Once the C3PAO submits the CMMC certificate to the DoD, your requirement for CMMC compliance has now been met.
To be eligible for a contract, your CMMC certification will be needed at the time of the award.
There are no fines for non-compliance; however, you will be unable to participate in DoD contracts.
Corserva is a CMMC-AB Registered Provider Organization™ (RPO)
 Corserva is a CMMC-AB Registered Provider Organization™ (RPO), and we are listed on the CMMC-AB Marketplace.
Corserva is a CMMC-AB Registered Provider Organization™ (RPO), and we are listed on the CMMC-AB Marketplace.
As an RPO, Corserva is authorized by the CMMC-AB to provide pre-assessment consulting services to DoD contractors and other Organizations Seeking Certification (OSC).
Corserva has created an easy process to enable you to get ready for a CMMC assessment and protect your government contracts. These are the steps we follow:
- Identify the relevant requirements of CMMC you will need to meet.
- Perform an "as is" gap analysis of your processes and security controls, identifying areas to be corrected.
- Create a list of remediation steps you will need to take before hiring a C3PAO to perform a CMMC assessment.
The end deliverable to you is a clear set of corrective actions to take to comply with CMMC.
Get started today by requesting a quote.
Get started today. Talk to a CMMC compliance expert by requesting a quote for CMMC consulting.