If you are looking for ways to improve your company’s cybersecurity, you have probably considered security information and event management (SIEM) solutions. But you may be feeling overwhelmed by the costs involved and the time commitment in implementation.
After all, if you already have a firewall and several other security tools in place within your IT infrastructure, why do you need a SIEM?
Why a Firewall is Not Enough
To better understand why you need a SIEM in addition to a firewall, it’s helpful to think about what a firewall is meant to do and how firewalls work.
In its most basic form, a firewall is meant to block inbound and outbound "connections," a connection being a traffic flow identifiable by a "tuple," or three specific parameters: the source IP address, destination IP address, and destination port.
By blocking connections, a firewall prevents things from taking place that shouldn't.
The most secure firewall you can have (and incidentally, the least expensive) is called an air gap — nothing can get in and nothing can go out.
However, in most cases an air gapped system is not capable of performing the business functions required by a company to make a profit, so a more expensive piece of electronic equipment is put in place instead. These devices often default to blocking all inbound traffic and allowing all outbound traffic. While allowing all outbound is a typical default, it is not a secure configuration.
Already the firewall has a problem.
Do I still need a firewall?
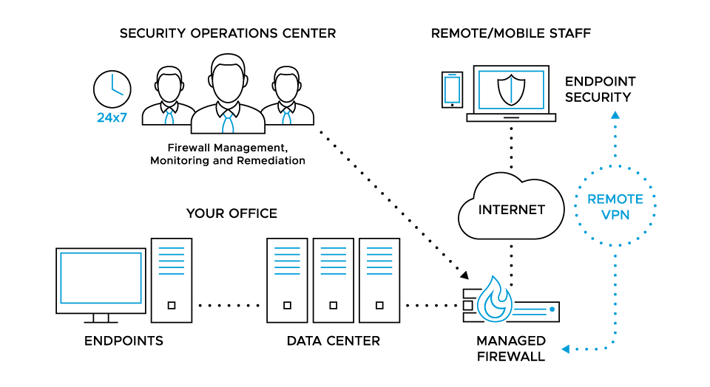
Yes, a SIEM doesn't replace your firewall. A firewall provides your first line of perimeter defense. The firewall allows or denies traffic in or out, while a SIEM analyzes log files.
A Typical Scenario
Consider the following scenario.
- The firewall is plugged in, people can watch their cat videos and life is good, except... where is my email?
- Oh! We need port 25 opened to allow traffic in to our mail server. So, you open it up.
- After going home that evening, you try to visit your company's website and realize, gosh darn, we need ports 80 and 443 opened.
- So you spin up Putty or OpenSSH and try to SSH to the firewall to make the change, only to realize that port 22 is also closed.
- A couple of days later you have it all figured out, a variety of ports are opened, you're filtering on sources and destinations, and things are working.
This scenario is a simplistic view of what takes place when a firewall is installed.
While a firewall is a valuable and effective security device, it has limits and does not block all the bad things trying to get in to your network. And more often than not (such as with the default configuration), it blocks none of the bad things going out, such as:
- SSH vulnerable to weak or reused passwords
- Web server vulnerable to SQL injection
- Workstations falling prey to Cryptomining
- Employees innocently uploading confidential information to a misconfigured Google share
But my firewall provides Unified Threat Management!
You have taken another step towards the preferred Defense in Depth security posture – that should be the goal.
The Intrusion Detection System (IDS) will see the use of Dropbox, Google Drive, and TOR. Reputation based URL filtering will help with drive-by JavaScript attacks, email filtering will help with phishing, and the latest machine learning endpoint security solution (EPS) will protect you from malware.
However, these also have holes and weaknesses — from IDS signatures that don’t recognize the latest attacks to human error where someone running with local admin rights ignores a warning and allows malware to run despite the red flag.
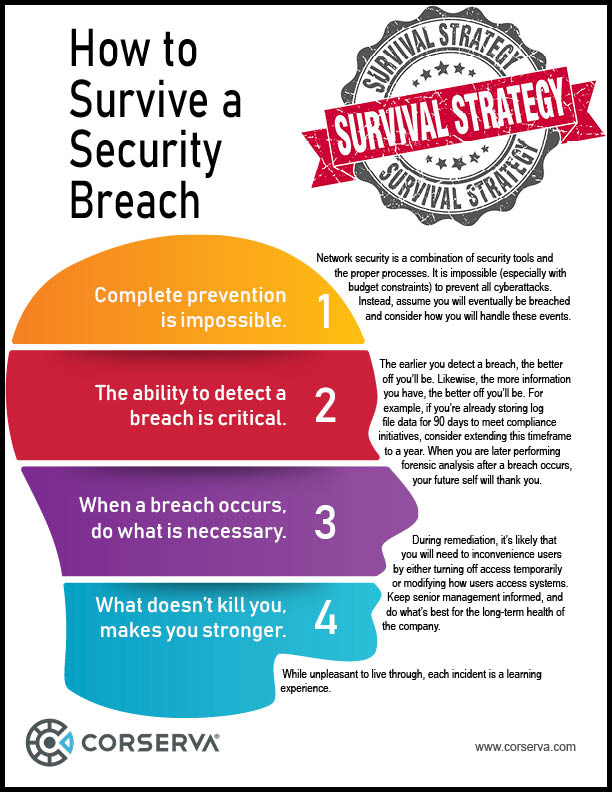
Absolute security is absolutely unobtainable.
Each of the steps you take gets you closer, but there is not enough money in the world to get all the way there.
"There are two types of companies: those that have been hacked, and those who don't know they have been hacked."
— John Chambers
former executive chairman and CEO of Cisco
If you can’t prevent all of the compromises, what you want to do is detect them.
Most companies spend a ton on prevention and ignore the detection side of the equation. Sure, the IDS is producing alerts, along with the antivirus engine, firewalls, and even the servers and workstations themselves. But who has time to look at all these logs? The logs are everywhere, there are hundreds of thousands of them, and there is no way to separate the important ones from the noise. The SIEM is a tool meant to help fill this critical gap.
How a SIEM Works
 Within your IT infrastructure, you may have several different devices that are generating log files. But if you are not looking at the logs on a regular basis, these logs are of little value. It’s probably not even humanly possible to look at all the logs. As the number of devices sending logs grows, it gets more and more difficult.
Within your IT infrastructure, you may have several different devices that are generating log files. But if you are not looking at the logs on a regular basis, these logs are of little value. It’s probably not even humanly possible to look at all the logs. As the number of devices sending logs grows, it gets more and more difficult.
A SIEM brings together the log data from disparate devices into a management layer, which provides visibility and the ability to detect and respond effectively to security breaches.
>> Grab your free SIEM success toolkit <<
But aren’t there other ways to review log files?
Years ago, your network security may have been limited to a firewall. It was a relatively easy task to review the logs manually, and maybe even daily.
Today, things are different.
You may have 50 different devices within your environment generating logs, such as:
- multiple firewalls
- web application filters
- IDS
- internet gateways
- DNS
- email filtering
- endpoint security
and more...
You can’t possibly look at all those logs on a regular basis. But a SIEM can, and most importantly, it can filter out the information you don’t need to look at and show you only what requires further analysis.
Some people who recognize the value in reviewing log files on a regular basis may use grep, spreadsheets, and other manual tools to filter the log information to try to identify issues that should be addressed (and filter out the unnecessary data). But this is an error-prone manual process. Also, this manual work usually cannot be done in a timely manner, and nothing close to real-time.
Why a SIEM is Better
A SIEM takes in log information from multiple devices, and then analyzes the data to look for patterns of malicious activity. Much of the information in the log files is normal behavior and can be ignored.
A SIEM triages the logs for you by analyzing all the log data, and through correlation rules, behavioral analysis, and machine learning, filters down and extracts events of interest. This much smaller event/alarm grouping now has a chance to be reviewed. Instead of looking at hundreds of thousands of events in the logs, you may only be looking at 10, those that have bubbled up to the top. Keep in mind that you still may look at some of the other data in those hundreds of thousands of events, but only in the context of the 10 flagged potential issues.
For example:
Without a SIEM, if you are reviewing the logs, you might see a failed login. On its own, that's not important. But if you see 20 failed logins followed by a successful login, that's the type of behavior that a SIEM will bubble up to the top. Any one of those single log events is not important, but the SIEM can identify the issue in the context of multiple events.
The SIEM is doing this work 24 hours a day, 7 days a week, 365 days a year. It’s looking at the logs constantly, so you will get an alert in real-time on only the important things. Whereas if you are manually reviewing the logs, your best case might be that you look at them once per day.
Configuring the SIEM
With a SIEM, there are certain rules already in place and new rules are created daily as it adapts to the changing world of threats. Typical alarms that get flagged include:
- Successful brute force attempts
- Communication (attempts) to known Command and Control (C2) sites
- Policy violations that could result in data loss
- Logons in the middle of the night
When using a SIEM, you also configure rules based on your unique business. Each company is different and needs a different set of rules.
For example:
You might need a rule such as "show me any file transfers from a server (Controlled Unclassified Information) to any site external to the company, except for these specific IP addresses belonging to a partner company."
These custom configuration rules are part of the process of tuning your SIEM.
Anatomy of an Attack
Let’s say an attacker sends an email to one of your employees who then clicks on a link.
The employee’s workstation will download that file, and your IDS will log that event as a file transfer.
The SIEM will see this in the log file data; if the file is an executable, the SIEM may flag that based on configuration rules.
Your antivirus software may also create a log that is sent to the SIEM.
At the same time, the workstation may log events that are reported to the SIEM, such as: if there is a suspicious DNS lookup, a process starts, or a program gets installed.
The SIEM will aggregate these events together and alert you to malware.
The SIEM provides an entire picture in real-time. It identifies the sequence of events that led to malware — something you could never get by manually reviewing logs on multiple devices.
By considering the timing of events from multiple sources, the SIEM can correlate the events that led to a security breach. Plus, it is common for attackers to try to remove or alter log entries to hide malicious activity; having an unalterable cache of log information stored on the SIEM can be vital.
Compliance Needs
Depending on industry mandates, you may need to be able to prove that you can answer questions such as “who logged on last week?” If you are saving the log files, you can comb through the information to answer these types of questions, but it won’t be easy or timely. On the other hand, with a SIEM, you can answer that question instantly.
Some compliance rules require that companies store log files, and a SIEM meets this need. Having a SIEM does make compliance easier, but the real value comes in identifying security breaches.
Protect – Detect – Respond
It can be helpful to think in terms of the simple security model of protect – detect – respond.
A firewall only protects.
A SIEM detects security breaches and provides the necessary information so you can then respond appropriately and recover quickly.
The SIEM stores all the log file data that is generated across your network. When a breach occurs, you have the information needed for forensic analysis. Because the SIEM makes it easy to sort, group, and filter the log data, you can pull log data from multiple sources, all related to a specific incident. You can’t get that type of insight with a manual process.
Not only does a SIEM identify a breach and enable you to recover from it quickly, you are now equipped with the information needed to create additional rules to prevent that type of breach occurring in the future.
Who needs to look at log files?
Depending on priorities and cybersecurity knowledge, different companies will leverage log files in different ways.
As described earlier, there may be many devices on the network creating log files. Some companies may not be storing log files because they don’t have a compliance reason to do so and because they don’t understand the value of the log data.
For compliance purposes, you can use a syslog server to store files. Compliance rules such as those for PCI, HIPAA, and NIST require that you store your log files. You may be storing log files to meet basic compliance needs but never looking at them if there are no resources available to do so.
You might fall into the category that you would like to review the logs, but you don’t have time for this manual process — it becomes a matter of priorities.
Do I still need a firewall?
Absolutely.
A firewall provides your first line of perimeter defense. It looks at traffic and creates logs reporting on the traffic that has been allowed through or that which has been blocked. Unlike a firewall, a SIEM doesn’t look at traffic; it looks at logs and analyzes that information looking for patterns. It cannot stop an attack by itself. To stop an attack a firewall rule or ACL is needed.
Defense in Depth
A firewall is a good first step to creating a secure IT environment, but it’s insufficient on its own. Best practices in cybersecurity, such as Defense in Depth, point to the need for multiple layers of security controls for redundancy purposes.
One example where a firewall falls short is with phishing or social engineering attacks. The firewall has no visibility into these and cannot prevent them. Through clever manipulation, an employee is persuaded to connect to a malicious website. The website launches a reverse shell of the client, and the attacker is inside. Once inside, the firewall's protections are limited.
It is here that defense in depth can either provide other ways to stop an attack or provide the logs and visibility that a SIEM needs to detect that something is wrong and there is a need for investigation.
The Cost Barrier
You may be discouraged by the high costs associated with the licensing, software, and hardware required for a SIEM solution. Not to mention the time investment to implement the solution and the personnel required to support it.
In the security model of protect – detect – respond, a SIEM solution will enable you to detect and respond to threats, but you need the security staff in place to manage the solution. SIEM is not a set-it-and-forget-it endeavor.
There is a better way.
Managed SIEM Services
A managed SIEM service provides you with the sophisticated cybersecurity capabilities of a SIEM, managed by cybersecurity experts for you. Managed SIEM pricing is based on the scope of your on-premise physical and virtual IT infrastructure, as well as how much log file data is generated from your network. Other considerations include how the security monitoring and remediation is to be performed, as well as the level of security engineers performing the work.
Corserva offers managed SIEM plans starting at $999/month.
>>> Request a quote for Managed SIEM <<<
Most plans provide real-time, round-the-clock security monitoring and alerting. Service level agreements (SLA) will dictate how quickly your managed security service provider (MSSP) will respond to security events. The level of response you require from your MSSP will impact costs. For example, you will pay less for a plan that limits remediation efforts to standard business hours than you will for a plan that provides 24x7x365 remediation.
With Corserva’s managed SIEM, you gain enterprise level cybersecurity for a fixed monthly cost, with no hefty licensing fees and no additional staffing requirements. We can accurately identify, contain, and remediate threats in your network. The security intelligence of the SIEM combined with our expertise enables us to detect and respond to security threats in your IT infrastructure.
Corserva offers a variety of cybersecurity solutions for businesses in addition to managed SIEM, such as managed firewall, email security, managed security as a service, and security awareness training.
Corserva’s staff have key security certifications including CISSP, CISM, CGE IT, CRISC, CEH, and CompTIA Security+. We provide 24x7x365 support for our clients from our US based security operations centers.
Request a quote for Corserva’s managed SIEM service.